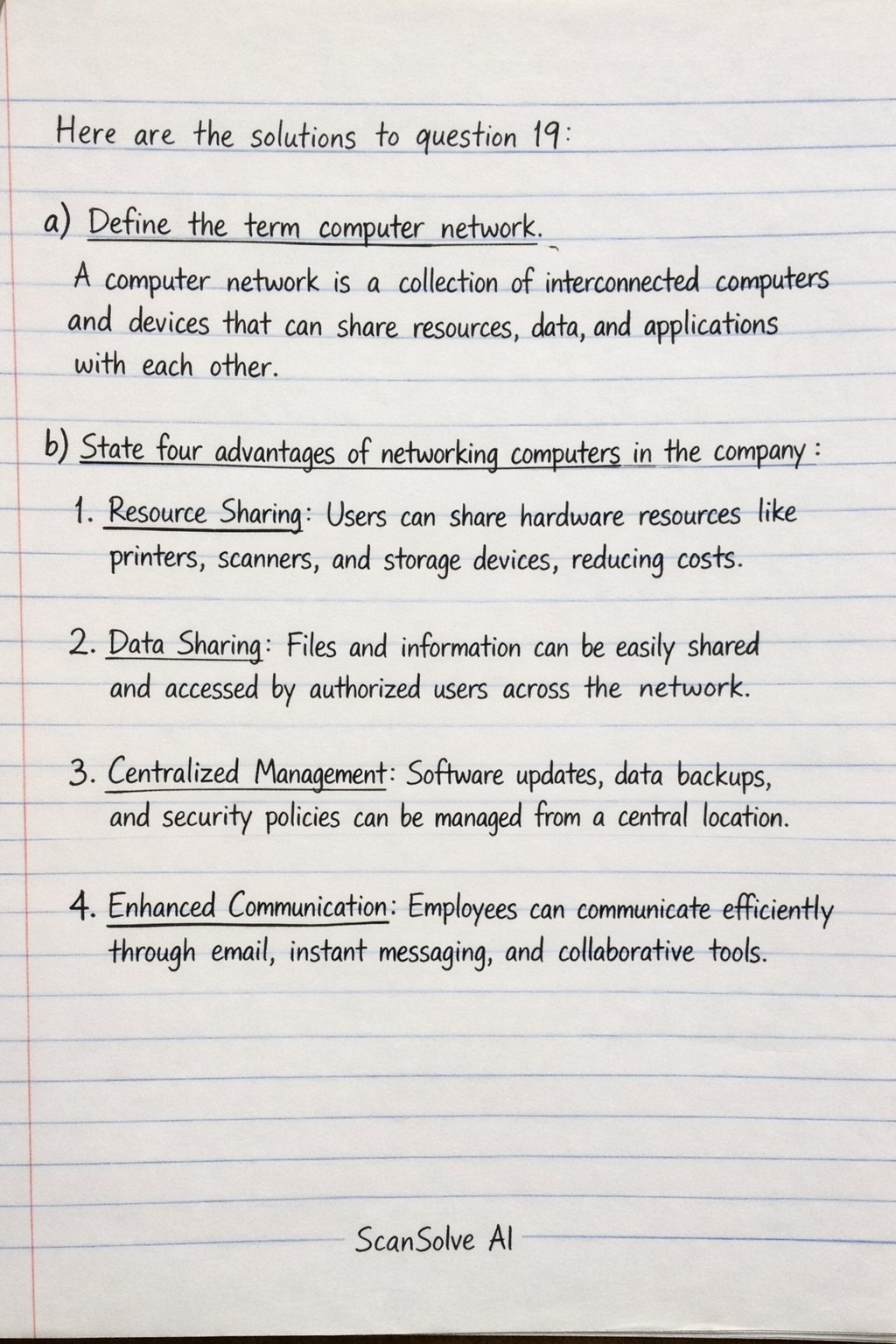
Here are the solutions to question 19: a) Define the term computer network. A computer network is a collection of interconnected computers and devices that can share resources, data, and applications with each other. b) State four advantages of networking computers in the company. 1. Resource Sharing: Users can share hardware resources like printers, scanners, and storage devices, reducing costs. 2. Data Sharing: Files and information can be easily shared and accessed by authorized users across the network. 3. Centralized Management: Software updates, data backups, and security policies can be managed from a central location. 4. Enhanced Communication: Employees can communicate efficiently through email, instant messaging, and collaborative tools. c) Explain four data security control measures that can protect customer data. 1. Encryption: Data is converted into a coded format to prevent unauthorized access. Even if intercepted, encrypted data is unreadable without the correct decryption key. 2. Access Control: Restricting who can access specific data and what actions they can perform (e.g., read, write, delete). This is often implemented using usernames, passwords, and role-based permissions. 3. Firewalls: A network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted internal network and untrusted external networks. 4. Regular Backups: Creating copies of data and storing them in a separate, secure location. This ensures that data can be recovered in case of loss due to hardware failure, cyber-attack, or accidental deletion. d) Differentiate between: i) Authentication and Authorization Authentication is the process of verifying the identity of a user or system. It confirms who* someone is, typically through credentials like usernames and passwords. Authorization is the process of determining what specific resources or actions an authenticated user or system is permitted to access or perform. It determines what* an authenticated user can do. ii) Physical security and Logical security Physical security refers to the protection of physical assets, such as computer hardware, servers, and network infrastructure, from unauthorized access, theft, damage, or environmental hazards. This includes measures like locks, surveillance cameras, and security guards. Logical security refers to the protection of data, software, and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction. This includes measures like passwords, encryption, firewalls, and access control lists.