This mathematics problem involves applying core mathematical principles and formulas. Below you will find a complete step-by-step solution with detailed explanations for each step, helping you understand not just the answer but the method behind it.

ScanSolve AI Answer
Here are the answers to your questions:
a) What does it mean? This statement means that despite advanced technological security measures, human error, negligence, or susceptibility to manipulation (like social engineering) often creates the most exploitable vulnerabilities in any security system. A strong security posture relies on every component, and if one component (the human) is weak, the entire system is at risk.
b) Why is it so? Humans are often the weakest link because they can be tricked, make mistakes, or bypass security protocols for convenience. Unlike machines that follow programmed rules, humans are susceptible to psychological manipulation (e.g., phishing, pretexting), forgetfulness (e.g., weak passwords), or lack of awareness regarding security best practices. This makes them a prime target for attackers seeking to bypass technical controls.
c) How do you mitigate such vulnerability? Mitigating this vulnerability involves a multi-faceted approach:
Last free one today — make it count tomorrow, or type /upgrade for unlimited.
Get instant step-by-step solutions to any question. Free to start.
Ask Your Question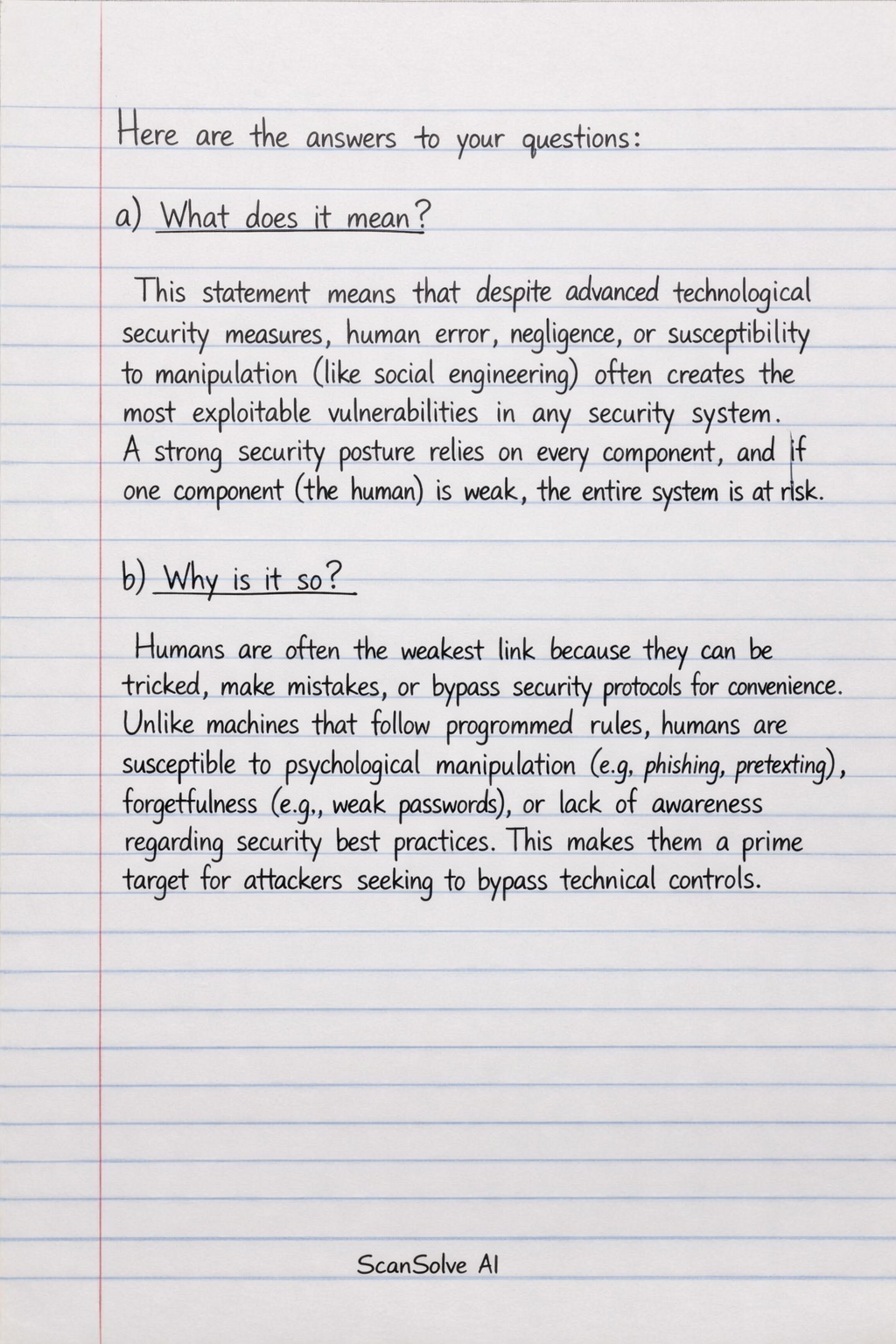
Handwritten Step-by-Step Solution
Get this as a handwritten image on WhatsApp — like a tutor wrote it for you.
Try on WhatsAppStill have questions?
a) What does it mean? This statement means that despite advanced technological security measures, human error, negligence, or susceptibility to manipulation (like social engineering) often creates the most exploitable vulnerabilities in any security s…
This mathematics problem involves applying core mathematical principles and formulas. Below you will find a complete step-by-step solution with detailed explanations for each step, helping you understand not just the answer but the method behind it.