This computer science problem involves algorithmic thinking and programming concepts. The solution below explains the approach, logic, and implementation step by step.

ScanSolve AI Answer
Here is a brief report on the WannaCry ransomware attack:
Overview of the attack: What happened? The WannaCry ransomware attack, which began on May 12, 2017, was a global cyberattack that encrypted data on computers running Microsoft Windows and demanded ransom payments in Bitcoin. It exploited a vulnerability in the Server Message Block (SMB) protocol.
Who was targeted? The attack targeted organizations and individuals worldwide, affecting over 200,000 computers in 150 countries. Notable victims included the UK's National Health Service (NHS), FedEx, Telefónica, and various government agencies and corporations.
Type of attack vectors with specific examples. The primary attack vector was the EternalBlue exploit, a vulnerability in Microsoft's SMB protocol, which allowed the ransomware to spread rapidly across networks. WannaCry also had worm capabilities, meaning it could self-propagate from one vulnerable computer to another without user interaction once it gained initial access to a network.
Impact: Financial, reputational, operational, etc. The impact was severe:
How was it solved? The rapid spread of WannaCry was significantly slowed by a security researcher who discovered and activated a "kill switch" domain embedded in the malware. Microsoft also released emergency security patches for older, unsupported Windows versions to mitigate the vulnerability. Organizations focused on isolating infected systems, applying patches, and restoring data from backups.
Lessons learned from the attack. Key lessons included the critical importance of patch management and regularly updating software to protect against known vulnerabilities. It highlighted the necessity of robust backup and recovery strategies to minimize data loss and downtime. The attack also underscored the need for network segmentation and strong cyber hygiene practices across all organizations.
That's 2 down. 3 left today — send the next one.
Get instant step-by-step solutions to any question. Free to start.
Ask Your Question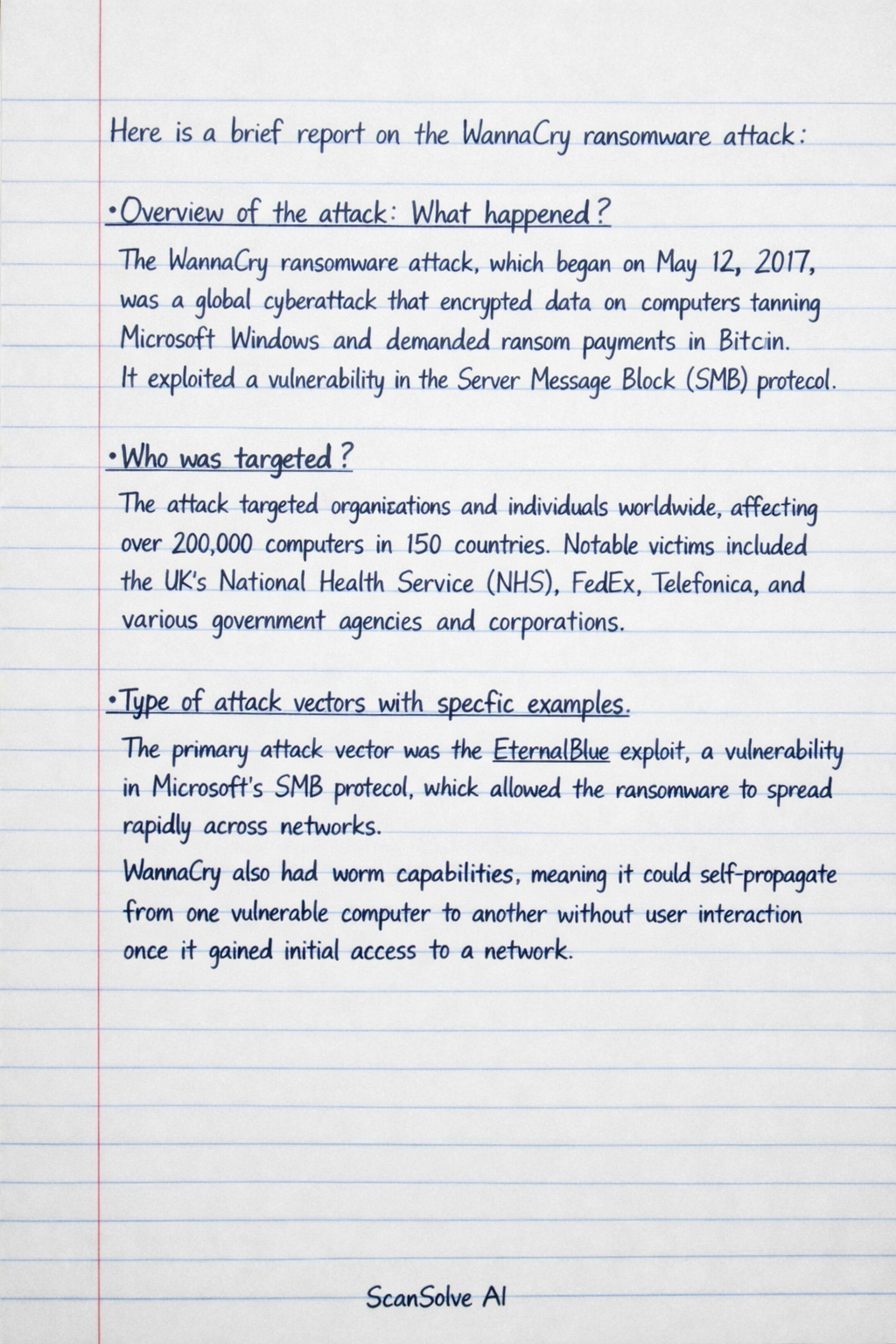
Handwritten Step-by-Step Solution
Get this as a handwritten image on WhatsApp — like a tutor wrote it for you.
Try on WhatsAppStill have questions?
Overview of the attack: What happened? The WannaCry ransomware attack, which began on May 12, 2017, was a global cyberattack that encrypted data on computers running Microsoft Windows and demanded ransom payments in Bitcoin.
This computer science problem involves algorithmic thinking and programming concepts. The solution below explains the approach, logic, and implementation step by step.