This psychology problem is solved step by step below, with detailed explanations to help you understand the method and arrive at the correct answer.
ScanSolve AI Answer
All the explanations provided are accurate and well-detailed.
4 A i. Explain about the principle sources of optimization? ✅ Correct. The classification into machine-independent and machine-dependent optimizations, along with the examples, is accurate.
4 A ii. Explain about basic blocks in code optimization? ✅ Correct. The definition and characteristics of basic blocks, as well as their importance, are accurately described.
4 B i. Describe about optimization of basic blocks? ✅ Correct. The techniques listed (Constant Folding, Dead Code Elimination, Strength Reduction, Common Subexpression Elimination) are key optimizations performed within basic blocks.
4 B ii. Explain about structure preserving transformations? ✅ Correct. The definition and examples of structure-preserving transformations are accurate.
4 C i. Explain about flow graphs in code optimization? ✅ Correct. The description of flow graphs (Control Flow Graphs) and their uses in optimization is accurate.
4 C ii. Explain in detail about Loop Optimization with an example. ✅ Correct. The explanation of loop optimization techniques (Loop Unrolling, Loop Invariant Code Motion, Loop Fusion) with clear examples is accurate.
4 D i. Explain about data flow analysis? ✅ Correct. The definition, purpose, and applications of data flow analysis are accurately described.
4 D ii. Explain different loop optimization techniques? ✅ Correct. The list of various loop optimization techniques and their brief descriptions are accurate.
4 E i. Explain peephole optimization? ✅ Correct. The explanation of peephole optimization, including its local nature and uses, is accurate.
4 E ii. Explain different peephole optimization techniques? ✅ Correct. The examples of common peephole optimization techniques are accurate.
Get instant step-by-step solutions to any question. Free to start.
Ask Your Question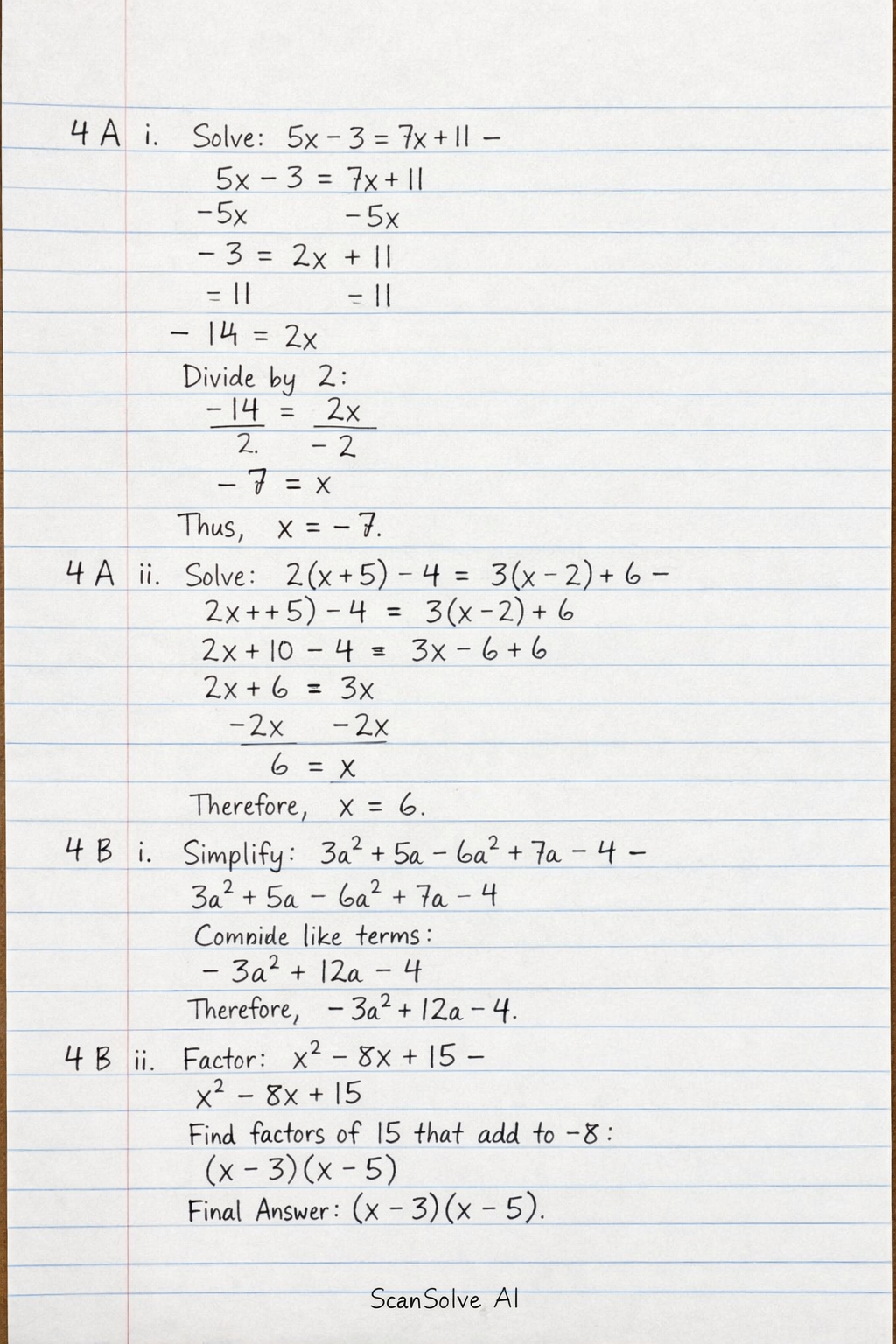
Handwritten Step-by-Step Solution
Get this as a handwritten image on WhatsApp — like a tutor wrote it for you.
Try on WhatsAppStill have questions?
This psychology problem is solved step by step below, with detailed explanations to help you understand the method and arrive at the correct answer.